[ad_1]
The rising recognition of on-line marketplaces has attracted fraudsters preying on unsuspecting patrons and sellers, seeking to rating cost card data slightly than to strike a discount. ESET researchers have discovered that one such organized scammer community – which makes use of Telekopye, a toolkit found by ESET Analysis in 2023 – has expanded its operations to focus on customers of well-liked lodging reserving platforms.
Final 12 months, we printed a two-part blogpost sequence on Telekopye, a Telegram-based toolkit cybercriminals use to rip-off individuals on on-line marketplaces. The first half targeted on Telekopye’s key options, whereas the second half examined the interior workings of the affiliated rip-off teams. On this blogpost, we observe up on what has modified in Telekopye operations since our final publication, based mostly on our continued monitoring. We glance into how these scammer teams have branched out to concentrating on Reserving.com and Airbnb, in addition to their numerous different efforts to optimize their operations and maximize monetary acquire. Final however not least, we offer steerage on the best way to keep protected against these scams.
We introduced our up to date findings on Telekopye on the Virus Bulletin convention on October 2nd, 2024, and in our white paper, which you’ll learn in full right here. The paper was additionally printed on the Virus Bulletin web site.
Key factors of this blogpost:
- ESET Analysis shares up to date findings on Telekopye, a rip-off toolkit designed to assist cybercriminals defraud individuals on on-line marketplaces.
- Whereas our earlier analysis explored the technical and organizational background of Telekopye scams, our newest analysis describes the scammers’ numerous efforts to maximise their monetary positive factors – increasing their sufferer pool, making the most of seasonal alternatives, and bettering their instruments and operations.
- Most notably, Telekopye teams have expanded their concentrating on to well-liked lodging reserving platforms, reminiscent of Reserving.com and Airbnb.
- This new rip-off situation comes with a concentrating on twist, using compromised accounts of professional resorts and lodging suppliers.
- These scams had been particularly prevalent in the summertime vacation season within the focused areas, surpassing Telekopye market scams, in keeping with ESET telemetry.
Telekopye overview
Telekopye is a toolkit that operates as a Telegram bot, primarily serving as a Swiss Military knife for turning on-line market scams into an organized illicit enterprise. It’s utilized by dozens of rip-off teams, with as much as hundreds of members, to steal thousands and thousands from Mammoths, as they name the focused patrons and sellers. Neanderthals, as we name the scammers, require little to no technical information – Telekopye takes care of the whole lot in a matter of seconds.
Found by ESET Analysis in 2023, Telekopye has been in use since no less than 2016, with victims everywhere in the world. A number of leads level to Russia because the nation of origin of the bot’s writer(s) and likewise the scammers utilizing it. Telekopye is designed to focus on a big number of on-line providers in Europe and North America, reminiscent of OLX, Vinted, eBay, Wallapop, and others. On the time of writing, we’ve got counted roughly 90 totally different providers being focused by the scams.
Neanderthals – members of any Telegram group using Telekopye – acquire entry to the bot’s UI, which allows easy technology of phishing emails, SMS messages, internet pages, and different options.
Telekopye teams have a business-like operation, with a transparent hierarchy, outlined roles, inside practices – together with admission and mentoring processes for newcomers – fastened working hours, and fee payouts for Telekopye directors. The Staff performing the scams should flip over any delicate data stolen, and don’t truly steal any cash – that’s managed by different roles within the group. Every group retains a clear chat of all transactions, seen to all members.
Neanderthals make the most of two essential situations for concentrating on on-line marketplaces – one the place they pose as sellers and one other, rather more frequent, the place they pose as patrons. Each situations finish with the sufferer/Mammoth coming into cost card data or on-line banking credentials right into a phishing internet web page mimicking a cost gateway.
Not too long ago, Telekopye teams have expanded their concentrating on by including help for scamming customers of well-liked on-line platforms for reserving lodging, which we cowl within the following part.
Branching out to lodging reserving platforms
In 2024, Telekopye teams have expanded their scamming playbook with schemes concentrating on customers of well-liked on-line platforms for resort and residence reservations, reminiscent of Reserving.com and Airbnb. They’ve additionally elevated the sophistication of their sufferer choice and concentrating on.
Concentrating on with a twist
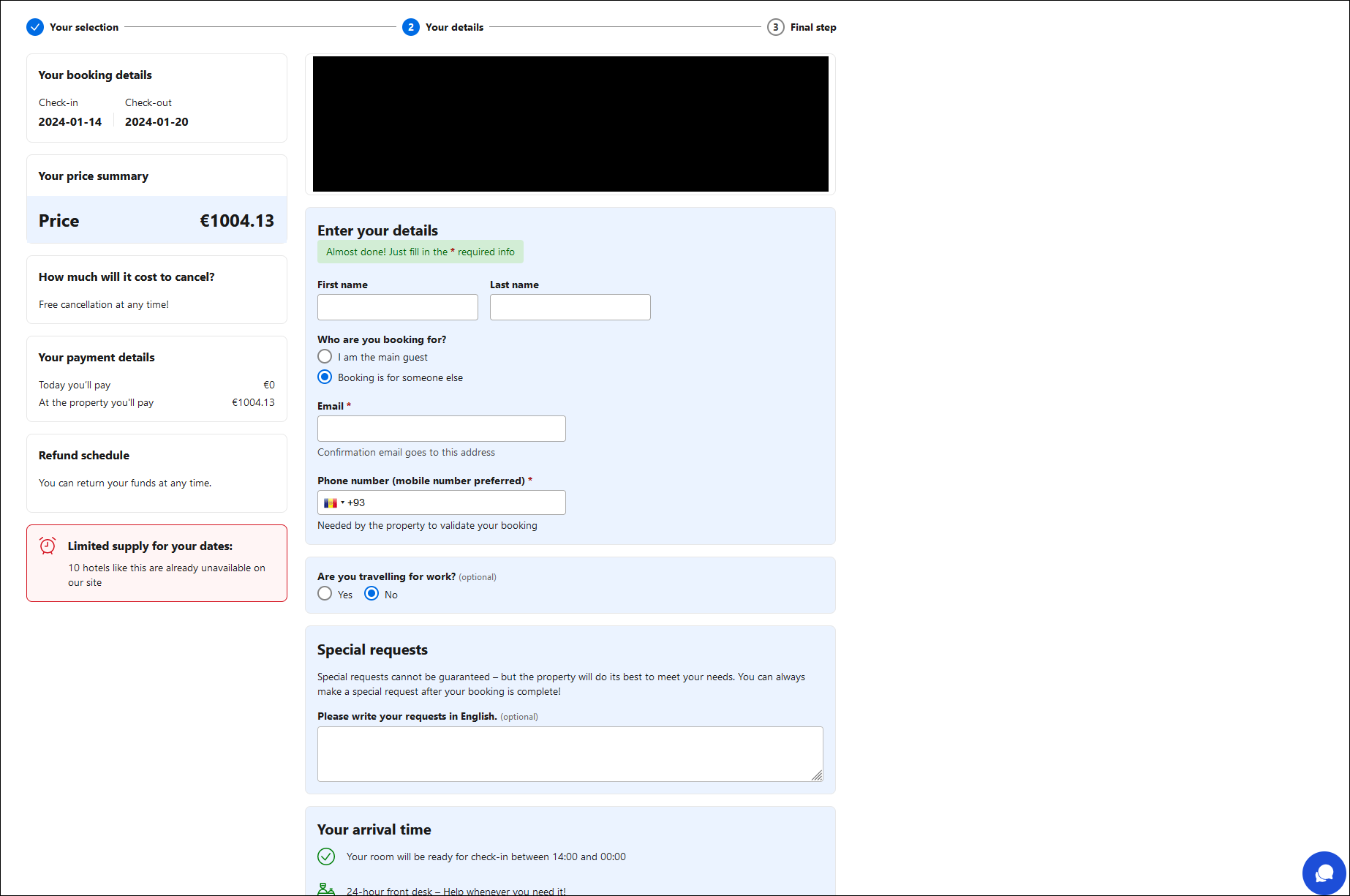
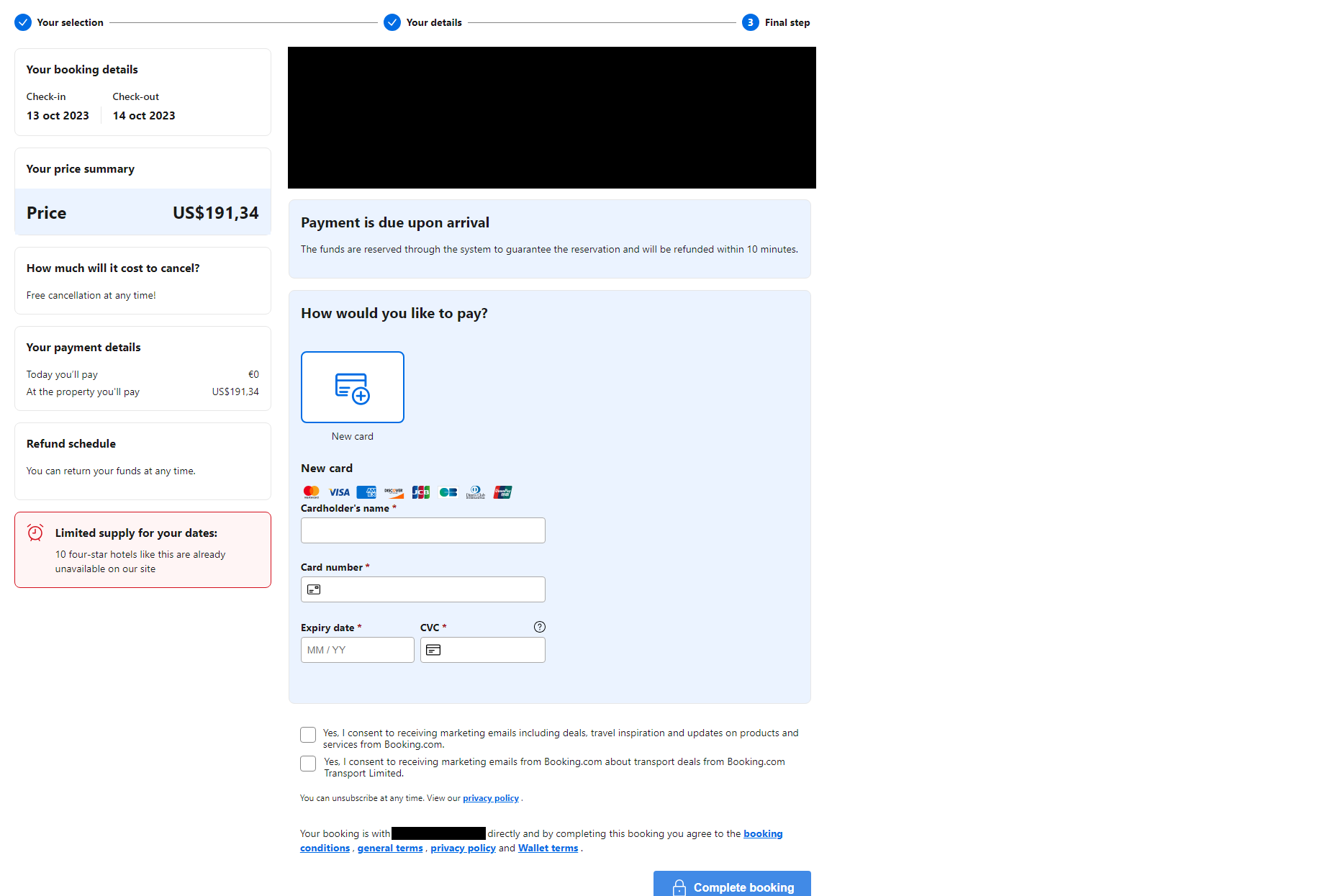
On this new rip-off situation, Neanderthals contact a focused person of certainly one of these platforms, claiming that there’s a difficulty with the person’s reserving cost. The message comprises a hyperlink to a well-crafted, legitimate-looking internet web page mimicking the abused platform.
The web page comprises prefilled details about a reserving, such because the check-in and checkout dates, value, and site. This comes with a troubling twist: the data supplied on the fraudulent pages matches actual bookings made by the focused customers.
The Neanderthals obtain this by using compromised accounts of professional resorts and lodging suppliers on the platforms, which they almost definitely entry by way of stolen credentials bought on cybercriminal boards. Utilizing their entry to those accounts, scammers single out customers who lately booked a keep and haven’t paid but – or paid very lately – and speak to them by way of in-platform chat. Relying on the platform and the Mammoth’s settings, this results in the Mammoth receiving an electronic mail or SMS from the reserving platform.
This makes the rip-off a lot more durable to identify, as the data supplied is personally related to the victims, arrives by way of the anticipated communication channel, and the linked, faux web sites look as anticipated. The one seen signal of one thing being amiss are the web sites’ URLs, which don’t match these of the impersonated, professional web sites. Neanderthals can also use their very own electronic mail addresses for the preliminary communication (slightly than the compromised accounts), wherein case the emails is perhaps extra simply acknowledged as malicious.
As soon as the goal fills out the shape on the phishing web page (Determine 1), they’re dropped at the ultimate step of the “reserving” – a type requesting cost card data (Determine 2). As within the market scams, card particulars entered into the shape are harvested by the Neanderthals and used to steal cash from the Mammoth’s card.
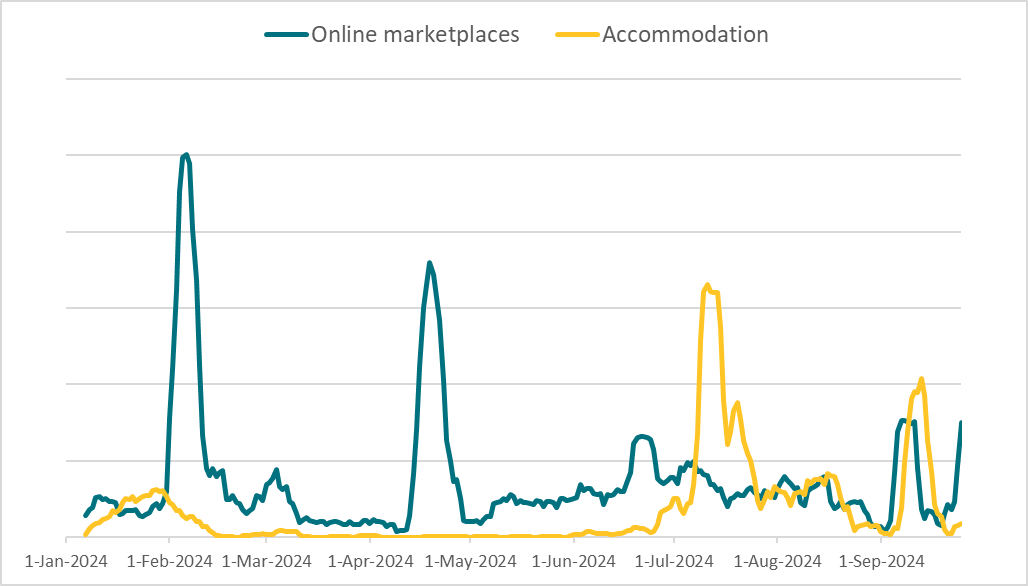
In keeping with ESET telemetry, such a rip-off began gaining traction in 2024. As seen in Determine 3, the accommodation-themed scams noticed a pointy uptick in July, surpassing the unique Telekopye market scams for the primary time, with greater than double the detections throughout that month. In August and September, the detection ranges for the 2 classes evened out.
As this enhance coincides with the summer time vacation season within the focused areas – prime time for making the most of individuals reserving stays – it stays to be seen whether or not this development will proceed. Trying on the general 2024 knowledge, we are able to see that these newer scams have amassed roughly half of the detection numbers of {the marketplace} variants. That is noteworthy contemplating that the newer scams concentrate on two platforms solely, in comparison with the wide range of on-line marketplaces focused by Telekopye.
Superior Telekopye options
Apart from diversifying their goal portfolio, Neanderthals have additionally improved their instruments and operations to extend their monetary returns.
All through our monitoring of Telekopye, we’ve noticed that totally different Telegram teams implement their very own superior options into the toolkit, aimed toward dashing up the rip-off course of, bettering communication with targets, defending phishing web sites in opposition to disruption by opponents, and different targets.
Automated phishing web page technology
To hurry up the method of making rip-off supplies for posing as patrons on marketplaces, Neanderthals applied internet scrapers for well-liked focused platforms. With these, solely the URL to the product is required, as an alternative of getting to manually fill out a questionnaire concerning the focused Mammoth and product in query. Telekopye parses the net web page and extracts all vital data robotically, offering a big speedup for the scammers.
Interactive chatbot with on-the-fly translation
Neanderthals keep a big assortment of predefined solutions to questions generally requested by Mammoths. These are translated into numerous languages and stored as a part of inside documentation, with the translations perfected through the years.
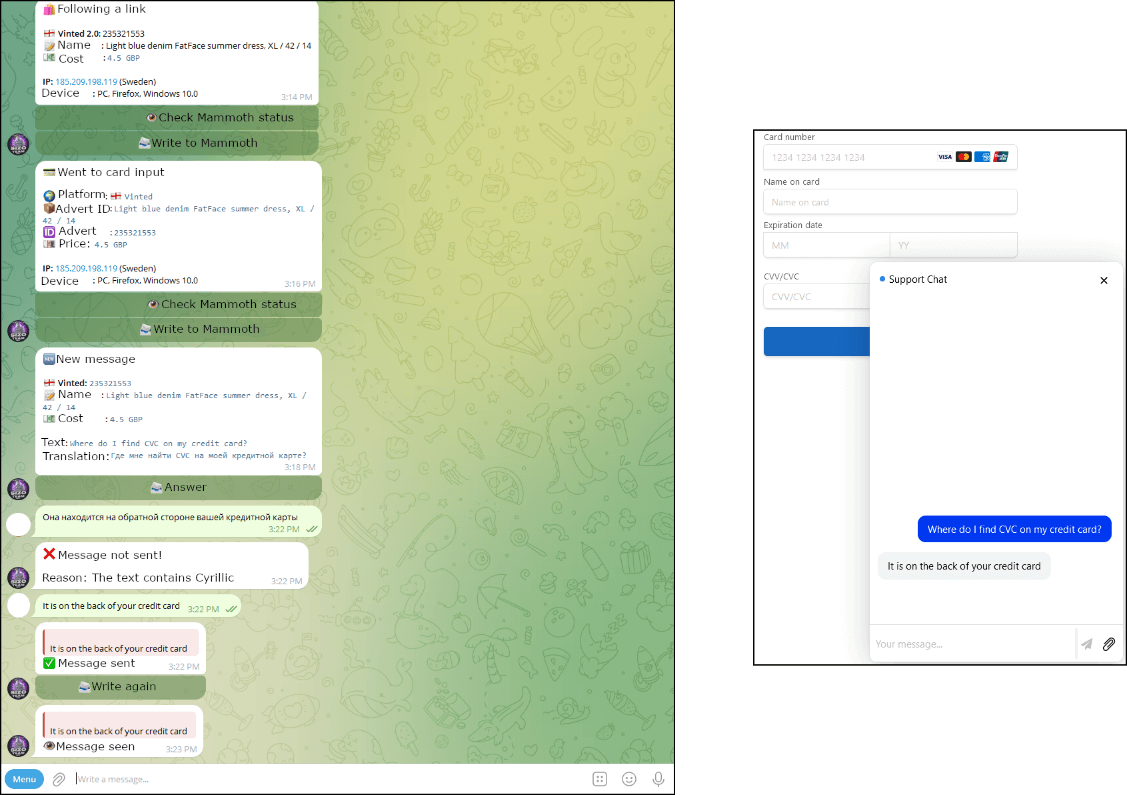
Neanderthals sometimes use these predefined phrases to attempt to direct the Mammoth to the phishing web site, which comes with a chatbot within the decrease proper nook. Any message the Mammoth enters into the chat is forwarded to the Neanderthal’s Telegram chat, the place it’s robotically translated. Automated translation of Neanderthals’ messages just isn’t supported – Neanderthals translate their messages manually, often utilizing DeepL. Determine 3 reveals how such an interplay appears from the Neanderthal’s and Mammoth’s factors of view.
Anti-DDoS measures
The overwhelming majority of the phishing web sites are serviced by Cloudflare, counting on that service’s added safety, primarily in opposition to crawlers and computerized evaluation. Curiously, among the Telekopye phishing web sites additionally include DDoS safety included. In keeping with the Neanderthals’ information base, which we obtained by infiltrating their ranks, this function goals to guard in opposition to assaults by rival teams. These are typically launched as a way to disrupt a competitor’s operations for a brief interval.
Regulation enforcement operations
In late 2023, after ESET Analysis had printed its two-part sequence on Telekopye, Czech and Ukrainian police arrested tens of cybercriminals using Telekopye, together with the important thing gamers, in two joint operations. Each operations had been aimed in opposition to an unspecified variety of Telekopye teams, which had collected no less than €5 million (roughly US$5.5 million) since 2021, based mostly on police estimates.
Apart from the apparent success in disrupting such legal actions, the arrests supplied new insights into the teams’ workings, most notably recruitment and employment practices. The teams in query had been managed, from devoted workspaces, by middle-aged males from Jap Europe and West and Central Asia. They recruited individuals in tough life conditions, by way of job portal postings promising “simple cash”, in addition to by concentrating on technically expert international college students at universities.
Some perpetrators confessed that in addition they participated in one other rip-off group, just like the Telekopye ones, that utilized name facilities. The police realized that the recruits in that operation had been usually stripped of their passports and private IDs to make quitting very tough. Additional, the managers typically went as far as to threaten the employees and their relations. This chilling growth places these operations into a very totally different gentle.
Suggestions
The easiest way to remain protected in opposition to scams pushed by Telekopye is being conscious of Neanderthals’ techniques and exercising warning on the affected platforms. Apart from realizing what pink flags to concentrate to, we strongly suggest utilizing a good antimalware answer in your gadget to step in for those who do find yourself being lured to a phishing web site.
On-line market scams
- At all times confirm the particular person you might be speaking with, primarily their historical past on the platform, age of their account, ranking, and site – a location too far-off, a recent account with no historical past, or a nasty ranking is perhaps indicators of a scammer.
- With the enhancements in machine translation, messages from a scammer won’t increase any pink flags when it comes to grammar. Moderately than specializing in the language, concentrate on the dialog itself – overly keen or assertive communication ought to increase some considerations.
- Maintain the communication on the platform, even when the particular person you’re speaking to suggests in any other case. Their unwillingness to remain on the platform ought to be a significant pink flag.
- If you’re a purchaser, use safe interfaces throughout the platform all through the entire shopping for course of, every time accessible. In any other case, insist on in-person alternate of products and cash, or prepare in your alternative of dependable supply providers with the choice to pay on supply.
- If you’re a vendor, use safe interfaces throughout the platform all through the entire promoting course of, every time accessible. In any other case, handle supply choices your self and don’t comply with these supplied by the client.
- For those who get to some extent the place you do go to a hyperlink despatched by the particular person you might be speaking to, be sure you fastidiously verify the URL, content material, and certificates properties of the web site earlier than participating with it.
Lodging reserving scams
- Earlier than filling out any types associated to your reserving, at all times ensure you haven’t left the official web site or app of the platform in query. Being directed to an exterior URL to proceed along with your reserving and cost is an indicator of a attainable rip-off.
- As a result of this rip-off makes use of compromised accounts of lodging suppliers, contacting the suppliers instantly just isn’t a dependable manner of verifying the legitimacy of cost requests. When doubtful, contact the official buyer help of the platform (Reserving.com, Airbnb) or report a safety difficulty (Reserving.com, Airbnb).
- To guard your account from compromise, whether or not you’re reserving lodging or renting one out, use a powerful password and allow two-factor authentication wherever accessible.
Conclusion
Our analysis into Telekopye actions has given us distinctive insights into these scams: we had been capable of perceive the technical means behind the scope of the operations, the enterprise facet of Telekopye teams, and even find out about Neanderthals themselves.
We’ve described the teams’ numerous efforts to maximise their monetary positive factors, together with increasing their sufferer pool, making the most of seasonal alternatives, and bettering their instruments and operations. Most notably, we’ve got detailed the Neanderthals’ latest strategy of concentrating on lodging reserving platforms, which additionally comes with extra subtle concentrating on.
It’s price noting that we’ve got communicated with a number of platforms focused by Telekopye all through our analysis; they’re absolutely conscious of those scams and confirmed they’ve employed a number of techniques to fight them. Nevertheless, warning continues to be suggested for customers as a result of variety of the scams and their steady evolution.
For any inquiries about our analysis printed on WeLiveSecurity, please contact us at threatintel@eset.com.ESET Analysis presents non-public APT intelligence studies and knowledge feeds. For any inquiries about this service, go to the ESET Risk Intelligence web page.
IoCs
Recordsdata
| SHA-1 | Filename | Detection | Description |
| E815A879F7F30FB492D4 |
rip-off.php | PHP/HackTool.Telekopye.B | Telekopye bot. |
| 378699D285325E905375 |
rip-off.php | PHP/HackTool.Telekopye.B | Telekopye bot. |
| 242CE4AF01E24DB05407 |
123.php | PHP/HackTool.Telekopye.A | Telekopye bot. |
| 9D1EE6043A8B6D81C328 |
mell.php | PHP/HackTool.Telekopye.B | Telekopye bot. |
| B0189F20983A891D0B9B |
neddoss.php | PHP/HackTool.Telekopye.A | Telekopye bot. |
| E39A30AD22C327BBBD2B |
nscode.php | PHP/HackTool.Telekopye.A | Telekopye bot. |
| 285E0573EF667C6FB7AE |
tinkoff.php | PHP/HackTool.Telekopye.A | Telekopye bot. |
Community
| IP | Area | Internet hosting supplier | First seen | Particulars |
| N/A | 3-dsecurepay[.]com | Cloudflare, Inc. | 2024-05-30 | Telekopye phishing area. |
| N/A | approveine[.]com | Cloudflare, Inc. | 2024-06-28 | Telekopye phishing area. |
| N/A | audittravelerbookdetails[.]com | Cloudflare, Inc. | 2024-06-01 | Telekopye phishing area. |
| N/A | btsdostavka-uz[.]ru | TIMEWEB-RU | 2024-01-02 | Telekopye phishing area. |
| N/A | burdchoureserdoc[.]com | Cloudflare, Inc. | 2024-05-31 | Telekopye phishing area. |
| N/A | check-629807-id[.]prime | Cloudflare, Inc. | 2024-05-30 | Telekopye phishing area. |
| N/A | contact-click2399[.]com | Cloudflare, Inc. | 2024-05-26 | Telekopye phishing area. |
| N/A | contact-click7773[.]com | Cloudflare, Inc. | 2024-05-30 | Telekopye phishing area. |
| N/A | get3ds-safe[.]information | Cloudflare, Inc. | 2024-05-31 | Telekopye phishing area. |
| N/A | hostelguest[.]com | Cloudflare, Inc. | 2024-05-30 | Telekopye phishing area. |
| N/A | order-9362[.]click on | Cloudflare, Inc. | 2024-05-29 | Telekopye phishing area. |
| N/A | shiptakes[.]information | Cloudflare, Inc. | 2024-05-29 | Telekopye phishing area. |
| N/A | quickroombook[.]com | Cloudflare, Inc. | 2024-06-02 | Telekopye phishing area. |
| N/A | validation-confi[.]information | Cloudflare, Inc. | 2024-05-29 | Telekopye phishing area. |
MITRE ATT&CK strategies
This desk was constructed utilizing model 15 of the MITRE ATT&CK framework.
| Tactic | ID | Identify | Description |
| Reconnaissance | T1589 | Collect Sufferer Id Info | Telekopye is used to collect cost card particulars, cellphone numbers, electronic mail addresses, and so forth. by way of phishing internet pages. |
| Useful resource Growth | T1583.001 | Purchase Infrastructure: Domains | Telekopye operators register their very own domains. |
| T1585 | Set up Accounts | Telekopye operators set up accounts at on-line marketplaces. | |
| T1585.002 | Set up Accounts: E-mail Accounts | Telekopye operators arrange electronic mail addresses related to the domains they register. | |
| T1586.002 | Compromise Accounts: E-mail Accounts | Telekopye operators use compromised electronic mail accounts to extend their stealthiness. | |
| T1587.001 | Develop Capabilities: Malware | Telekopye is customized malware. | |
| T1588.002 | Receive Capabilities: Software | Telekopye operators use extra bots to launder cash, scrape market analysis, and implement DDoS safety. | |
| Preliminary Entry | T1566.002 | Phishing: Spearphishing Hyperlink | Telekopye sends electronic mail or SMS messages that include hyperlinks to phishing web sites. |
| Assortment | T1056.003 | Enter Seize: Internet Portal Seize | Internet pages created by Telekopye seize delicate data and report it to the operators. |
[ad_2]